
PROTECT YOUR COMPUTER FROM TROJANS HORSES
HOW IT WORKS
01
WHAT IS A TROJAN HORSE
02
CHARACTERISTICS
03
EASY
A Trojan horse is one of the main types of malware. It is malware that infects your computer hidden as another application. It is really effective because you think that it is a normal or legitimate application and open it, but it reality it is an trojan horse that steals information from your computer.
I'm a paragraph. Click here to add your own text and edit me. It’s easy. Just click “Edit Text” or double click me to add your own content and make changes to the font. Feel free to drag and drop me anywhere you like on your page. I’m a great place for you to tell a story and let your users know a little more about you.
I'm a paragraph. Click here to add your own text and edit me. It’s easy. Just click “Edit Text” or double click me to add your own content and make changes to the font. Feel free to drag and drop me anywhere you like on your page. I’m a great place for you to tell a story and let your users know a little more about you.


What is a Trojan Horse?
01
WHAT IS A TROJAN HORSE?
A Trojan horse is one of the main types of malware. It is malware that infects your computer hidden as another application. It is really effective because you think that it is a normal or legitimate application and open it, but it reality it is an trojan horse that steals information from your computer.
02
CHARACTERISTICS
The main characteristic of a trojan horse is that is does not it does not replicate itself on your computer and transfer itself onto other computers. Also it is one of the only viruses that creates a backdoor on your computer.
03
THE IMPACT ON USERS
Once installed, the seemingly trustful website will actually open a backdoor on you computer. This backdoor will deal damage to the computer from the inside. But trojans are better than viruses because they don't replicate.
Our Product



MAIN IDEA
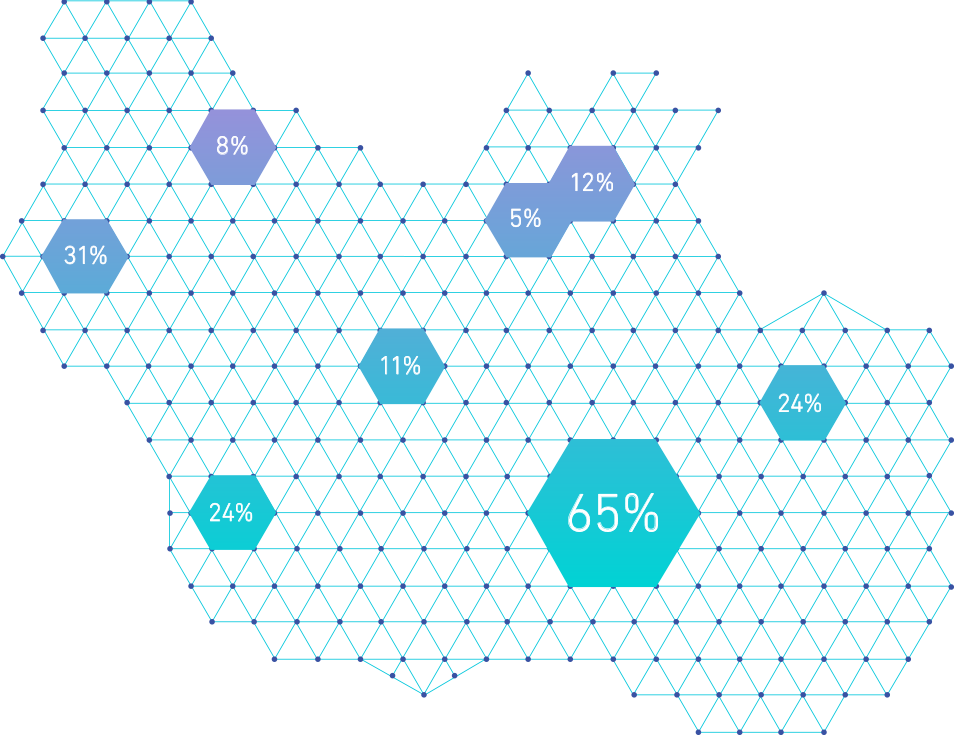
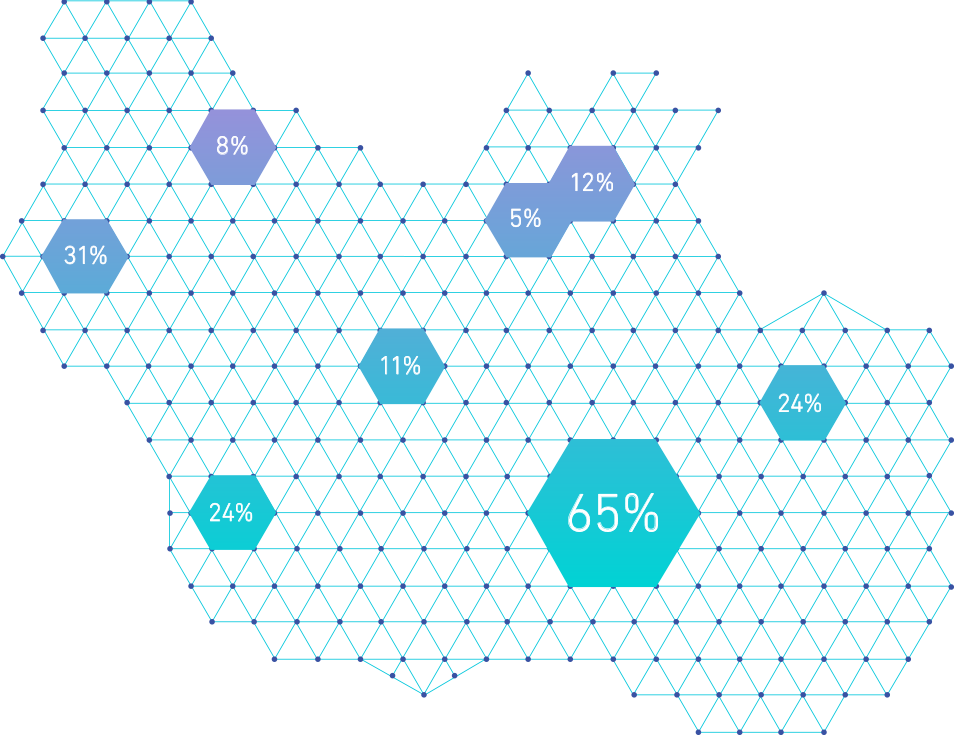
Our product is a malicious file and content detection system, primarily focused on trojans. Our product will be installed on the computer and check files or any content for trojan horses immediately after downloaded.
OUR APPROACH
Our application focuses on trojans because we feel that that is the most commonly used malicious type that infects people's computers. We feel that the approach of focusing only on trojans is better than trying to do the broad topic of malware because we are going for quality, not quantity. By only doing one type of malware, we can focus on making our software for this type perfect.
OUR SOFTWARE IN ACTION
When our product scans the file and, for example, a trojan is detected on the file, the system will send a message to the person through e-mail and will put a message on screen to alert the person immediately. The next step is to download a credible anti-virus system to try to fix it.
OUR COMPETITORS

.png)
.png)

.png)
CODE ANALYZATION
The technical level of the trojan horse is quite smart. The way it works is that when a user opens a file that contains a trojan horse, the trojan horse inside the file makes a copy of the unix shell and then sends it to the attacker through a relay server. This allows the attacker to gain control of your computer. This means they can get your passwords and any other important information you might have. The trojan horse is like the bridge between your computer and whoever is trying to attack you.
User downloads something with a trojan horse
This is a relay server that is connected from your computer to the attacker.
This is done by the trojan.
You now have a trojan horse in your computer
The attacker takes information from the user by the relay server.
This is the attackers computer that is connected to yours/
REAL-WORLD EXAMPLES